
Deep CDR

Deep CDR
Disarmament and reconstruction of deep content Advanced prevention of known and unknown threats
Comprehensive protection against known and unknown threats, zero-day attacks, advanced persistent threats (APTs) and sophisticated malware that gets out of control.
Can malware bypass Your security and infiltrate the system?
In the fight against malware, traditional preventive controls used by enterprises are often passive and considered inadequate because they rely on detecting bad activities and malicious code.
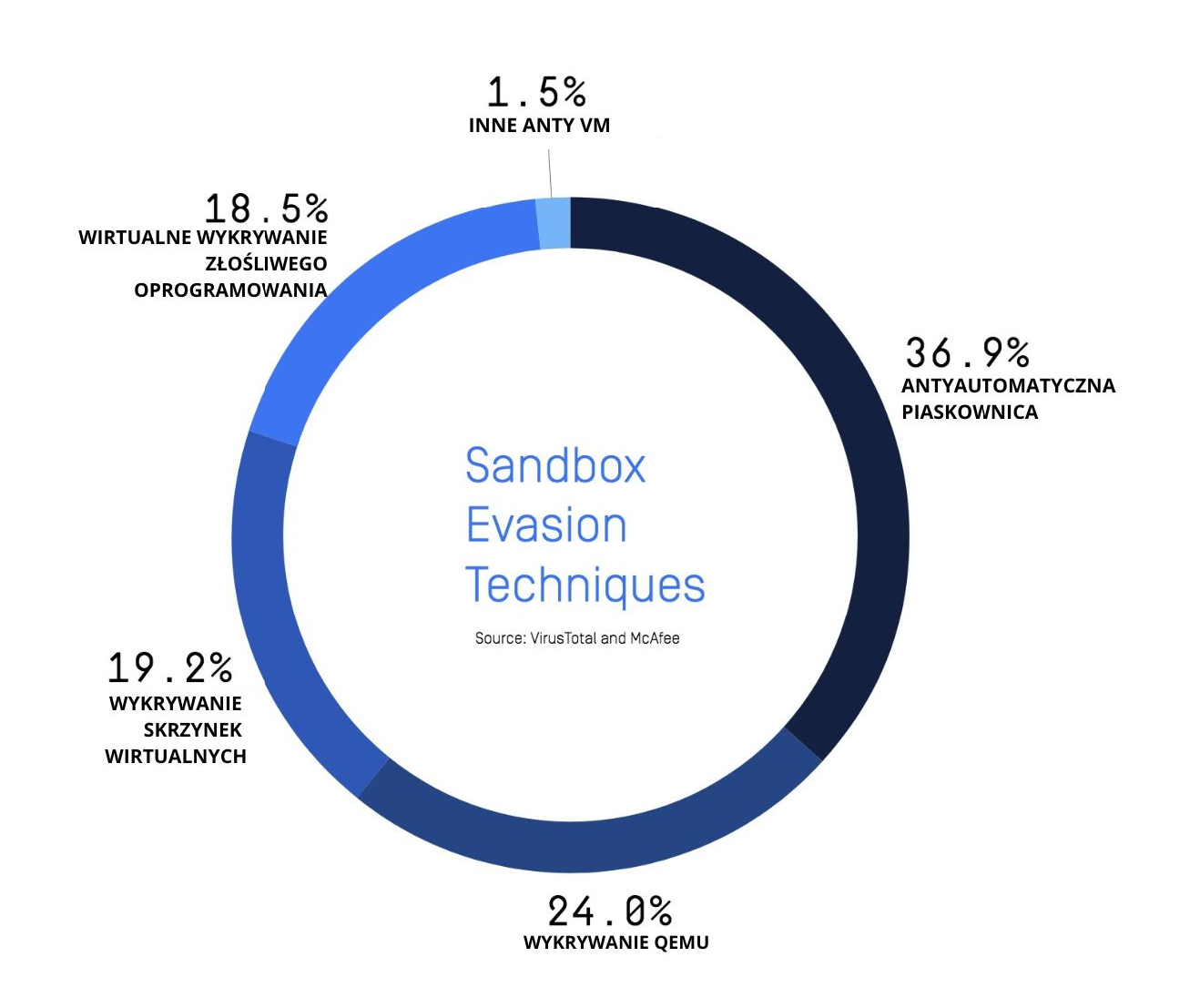
Malware is becoming more complex and increasingly effective at bypassing traditional and next-generation malware protection engines and sandboxes. Zero-day malware can easily defeat signature-based antivirus programs that detect only known threats.
Enterprises need a comprehensive threat prevention solution that does not rely on detection.

Deep CDR technology presentation
What is CDR technology?
Content Disarm & Reconstruction (CDR), also known as data sanitization, assumes that all files are malicious and cleans and rebuilds each file, ensuring full usability with secure content.
By cleaning up each file and removing any potential embedded threats, CDR (content disarming and reconstruction) effectively “disarms” all file-based threats, including – known and unknown; complex and sandbox-aware threats; and threats that feature malware-avoidance technologies such as completely undetectable malware, VMware detection, obfuscation and more.
OPSWAT Deep CDR
OPSWAT Deep CDR technology is a market leader offering excellent features such as multi-level archive processing, file regeneration accuracy and support for more than 100 file types.
We provide detailed information on what is being disinfected and how – allowing you to make informed choices and define configurations to suit your use case.
We deliver secure files where 100% of threats are eliminated within milliseconds, so your workflow is not interrupted.


Key differentiating factors
- Supports a wide range of file formats (more than 100), including regional formats such as JTD and HWP
- Recursive cleanup of complex files such as nested archives, embedded documents, email attachments and hyperlinks
- Offers flexible configuration options for each file format, allowing the administrator to enable or disable embedded objects that should be removed or cleaned up
- Preserves usability and functionality of files after cleanup
- Provides detailed reports on decontaminated components, accessible through the API, but also visible in the management console
- Integration with OPSWAT Multiscanning, including advanced threat detection
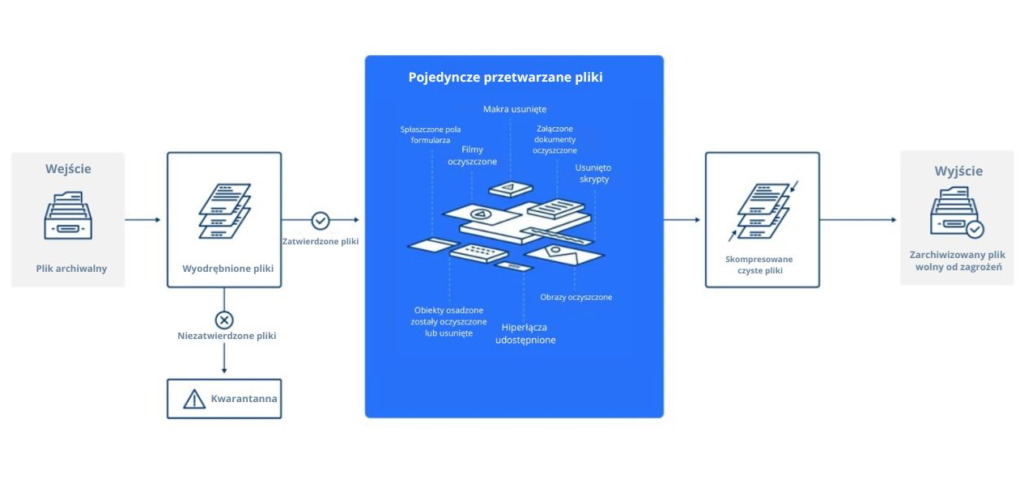
How Deep CDR works
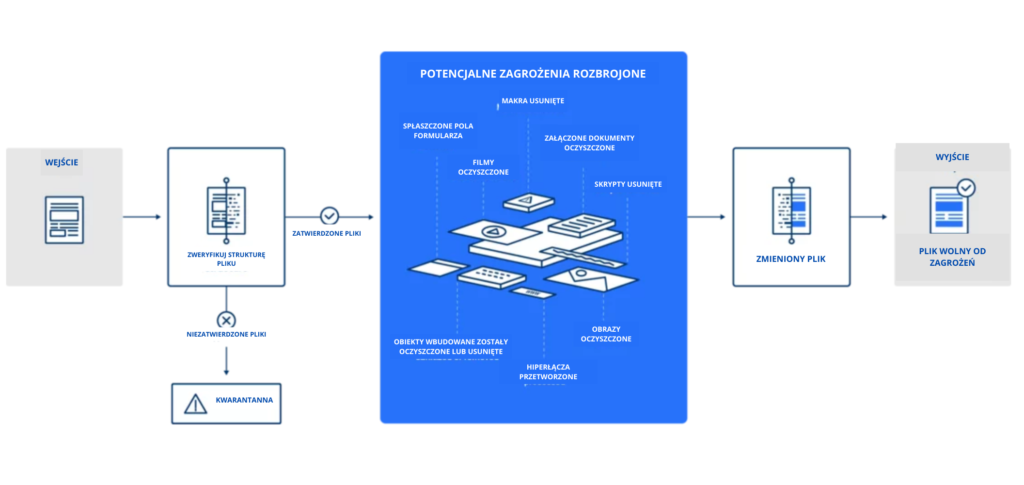
1 Files are evaluated and verified when they enter the purification system to ensure file type and consistency. File extensions are examined so that seemingly complex files don’t look simpler and flagged as malicious content, alerting organizations when they are under attack.
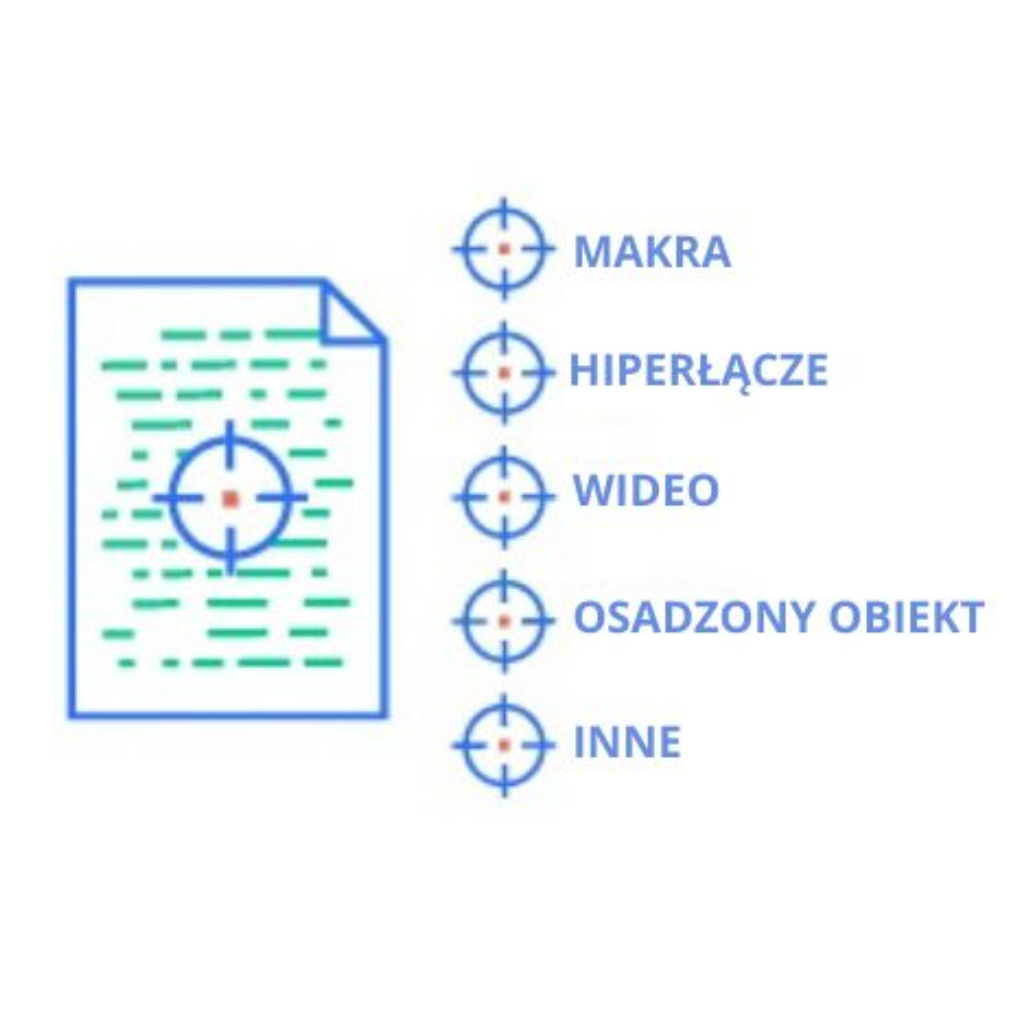
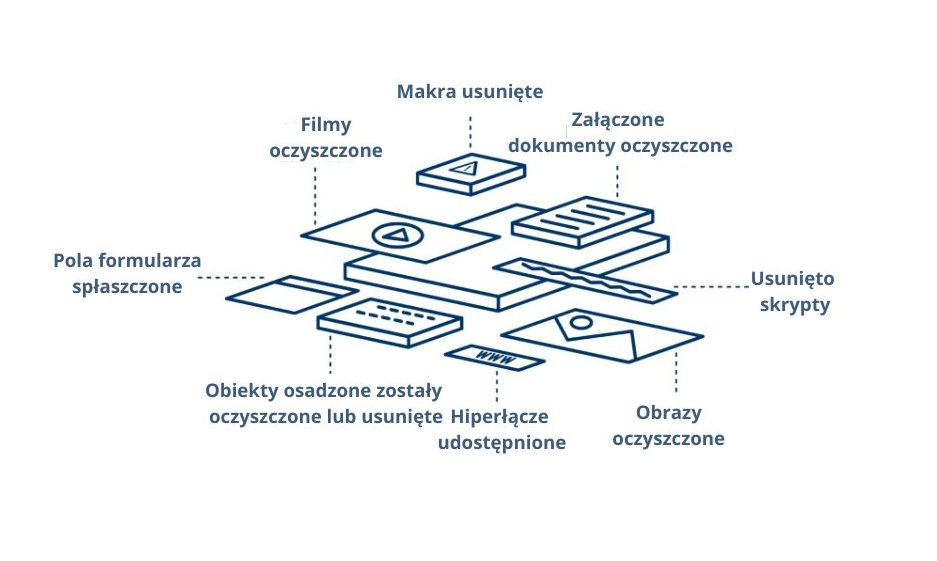
2. file elements are separated into separate components, and malicious elements are removed or cleaned up.
3. files are rebuilt in a fast and secure process. Metadata and all file features are reconstructed.

4 New files are recompiled, renamed and delivered – maintaining the integrity of the file structure, so users can safely use the file without losing usability.
Deep CDR / data cleansing process
Single document
Archive file
Features and benefits
More than 100 supported file types
Clean and reconstruct more than 100 popular file types, ensuring that each file is fully usable with safe content. Supported file types include PDF, Microsoft Office, HTML and many image files. Language/region specific file formats such as JTD and HWP files are also supported.
Over 200 file conversion options
Configurable file conversion allows you to change files to different formats (e.g., convert a .jpg file to a .bmp file, then to a .pdf file, then back to .jpg). Many conversions prevent document-based threats from entering highly secure networks.
4500+ file type verifications
Verify more than 4,500 file types to combat fake file attacks and detect seemingly complex files that look nothing like simpler ones.
Performance x30
For fast and effective prevention, Deep CDR is on average 30 times faster than sandboxed analysis and prevents malware (including zero-day) that was designed to evade sandboxed detection.
Integration with more than 30 engines
Integrates with OPSWAT Multiscanning, alerting users if they are under attack. It provides visibility across channels and points of entry for files, including email attachments, files on mobile media devices and browser downloads – enhancing security across the organization.
Configurable workflow
Customize the order of Multiscanning and Deep CDR steps for different file entry points. Depending on the channels from which the files originated, you may want to clean up the external files first, provide users with a cleaned-up version, and then scan the original files for full visibility of the attack matrix.



