
File transfer security
Discussion of file transfer security
File transfer is essential to the effective operation of an organization and is needed for collaboration among the organization’s employees and to increase user productivity. They are a critical component of most Internet applications and services. However, they pose a serious security threat, as cybercriminals can compromise your servers or your entire system by sending malicious files.
Traditional detection and prevention mechanisms are insufficient to prevent cybercriminals from attempting to upload malicious content to penetrate your environment and steal your data.
Integrating the many solutions needed to assess suspicious files and detect leaks of confidential data is costly and time-consuming.
Enterprises need a robust layer of protection between the files they transfer and their network.
Why you need file transfer security protection
Protect your users
Attackers can target end users and infect their systems. They can steal sensitive information and personally identifiable information from them.
Your collaboration and hosting platform may inadvertently host and distribute malicious samples that may contain illegal, offensive or copyrighted content/data, resulting in regulatory fines, costly lawsuits and bad publicity.
Protect your critical infrastructure
Hackers can bypass security and upload a new file or overwrite an existing file, which can be used to launch a server-side attack. They can then take control of your server and data, disable your site/app, use you for ransom, sell/disclose sensitive information, or upload more malicious files to your system.
If a very large file (multi-level archives, etc.) is uploaded, it can cause heavy consumption of server resources and disrupt the service.

How can OPSWAT help manage file transfer security?
Zero-day and advanced malware protection
Zero-day attacks, advanced persistent threats (APTs) and sophisticated malware can be hidden in harmless files and bypass traditional antivirus solutions.
OPSWAT Deep CDR (Content Disarm and Reconstruction) technology cleans up more than 100 popular file types to prevent both known and unknown threats – including threats equipped with malware-avoidance technology such as completely undetectable malware, VMware detection, obfuscation and more. The resulting outputs are safe-to-use files for end users.
Preventing data loss
Detect, block and redact sensitive and proprietary data such as credit card numbers and social security numbers.
Check the contents of more than 40 popular file types for confidential data and personal information (PII) with Proactive DLP (Data Loss Prevention) technology and prevent potential data breaches and regulatory violations.
Meet compliance requirements
Regulatory rules are enforced to minimize breaches and privacy violations. Meeting compliance requirements is time-consuming and can be costly. If requirements such as HIPAA, RODO, PCI-DSS, etc. If they are not met, it can result in significant fines and penalties.
OPSWAT’s technologies provide compliant processes, comprehensive visibility and detailed reporting capabilities that help meet the requirements of OWASP guidelines.
Detection and prevention of malware
OPSWAT delivers proprietary Multiscanning technology, and is the known leader in the industry and proactively detects 99%+ of known malware threats by using signatures, heuristics, NGAV, and machine learning.
Simultaneous analysis leveraging the combined threat prevention of 30+ antimalware engines is an advanced threat detection and prevention technology that increases detection rates, decreases outbreak detection times and provides resiliency to anti-malware vendor issues.
Assess vulnerabilities before deployment
Uploaded files can trigger vulnerabilities in broken libraries or applications. Organizations are increasingly vulnerable to attacks during the detection window, when an application is installed and when a vulnerability is detected. OPSWAT File-based Vulnerability Assessment – scans and analyzes binaries and installers uploaded via the website to detect known application vulnerabilities before they are installed or deployed.
File transfer security assessment
OPSWAT Professional Services can quickly assess readiness to secure file transfers. We tailor the assessment to your organization’s specific needs based on our proven methodology, and then provide a detailed analysis report with further discussion and recommendations.





OPSWAT PROVIDES EVERYTHING YOU NEED TO SECURE FILE TRANSFERS:
Visibility
Instantly monitor and assess security status and potential threats. A real-time dashboard immediately alerts you to potential threats and resource gaps. Drill deeper to investigate any areas of concern and take corrective action.

High performance and scalability
Fast scanning and reconstruction of files in milliseconds without affecting performance. Scalability to any volume with our built-in high performance architecture and load balancing features.

Simple and flexible implementation
Fast and scalable local and cloud implementation using REST API or any product that supports ICAP (Internet Content Adaptation Protocol).
Support for multiple platforms (Windows, Linux) and multiple deployment modes (Docker, Cloud, Datacenter).

What do we offer?
Integration with REST API
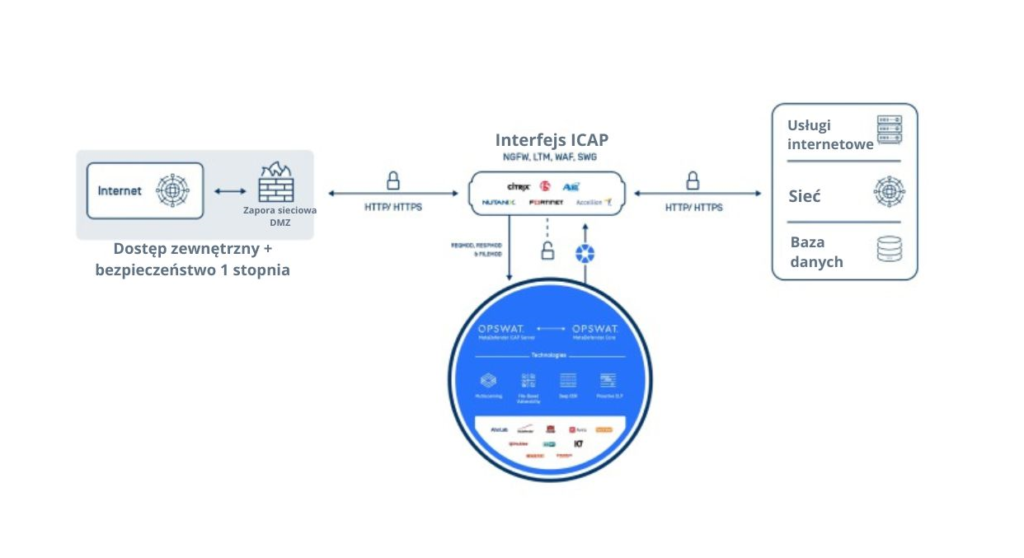
ICAP interface



