MetaDefender Cloud
MetaDefender Cloud-Ramsdata.
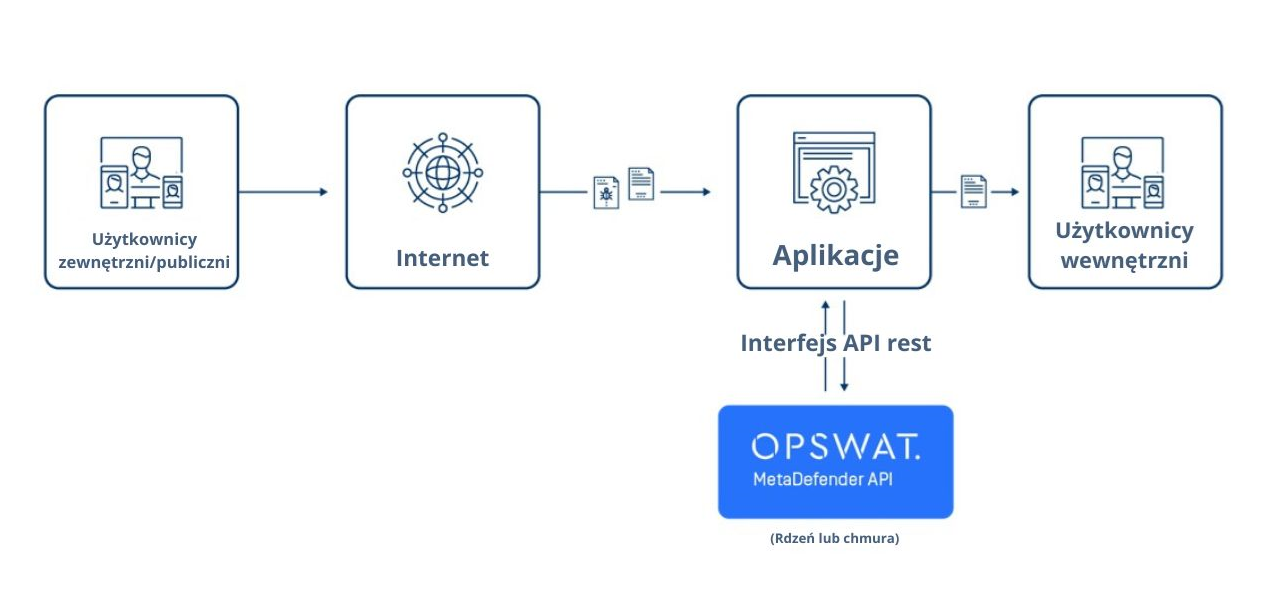
Cloud-based advanced threat protection and malware analysis. The MetaDefender Cloud API provides enterprise malware researchers, incident response teams and technology providers with comprehensive APIs to leverage advanced threat detection and prevention technologies.
Using our REST API, organizations can easily add cloud-based detection and prevention of cybersecurity threats using Deep CDR and multiscanning with more than 20 malware protection engines. Our “Don’t trust files” philosophy led us to develop a cloud platform designed to secure organizations from file-based attacks.
Analyze suspicious files and URLs
Files are still the main attack vector used today. Organizations using critical infrastructure must take strong preventive measures in their daily operations to protect themselves from attacks. CISOs and SOCs face great challenges to keep their organizations’ security up-to-date using the latest industry best practices. OPSWAT creates market-leading technologies with malware detection and prevention features. MetaDefender Cloud makes OPSWAT technologies available in a comprehensive cloud service, quickly and highly available.

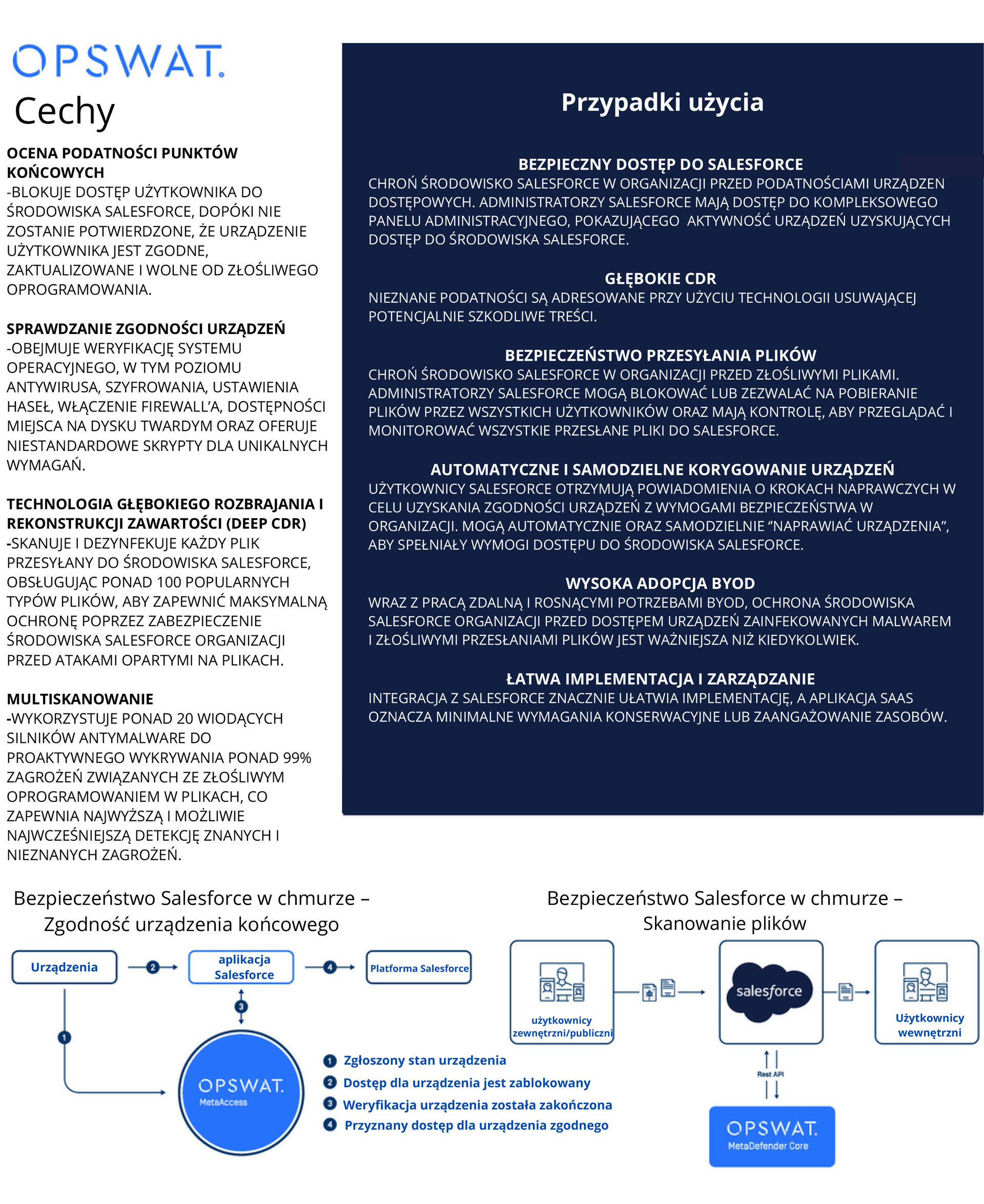
MetaDefender Cloud presentation – Technologies
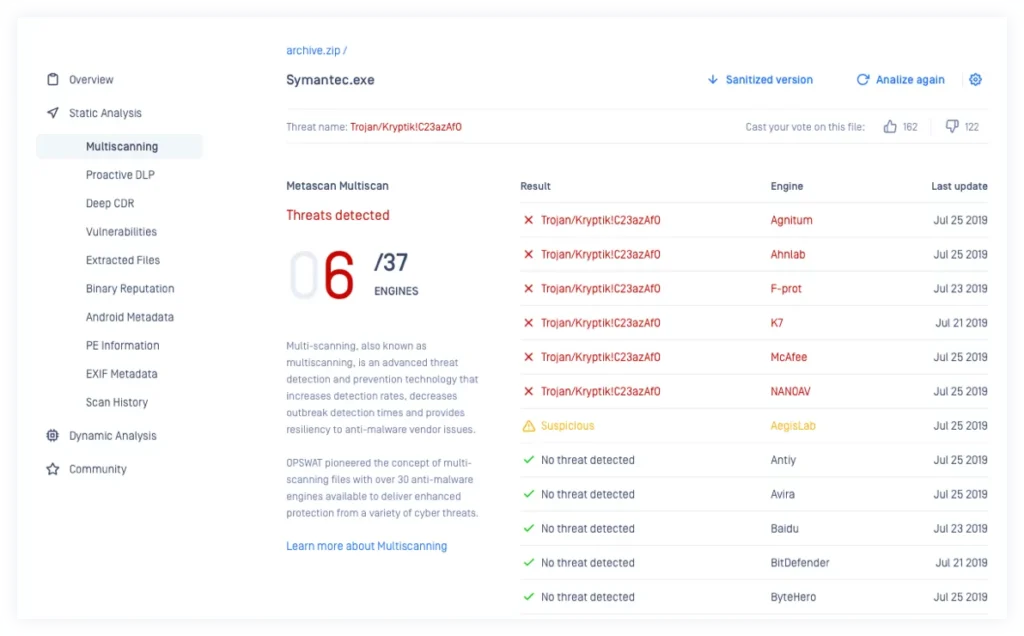
Multiscanning
Increase detection rates, reduce outbreak detection times, and provide resilience to malware protection software vendors. Simultaneous analysis using more than 20 industry-leading malware protection engines, such as McAfee, Kaspersky or Bitdefender, using signatures, heuristics and machine learning.
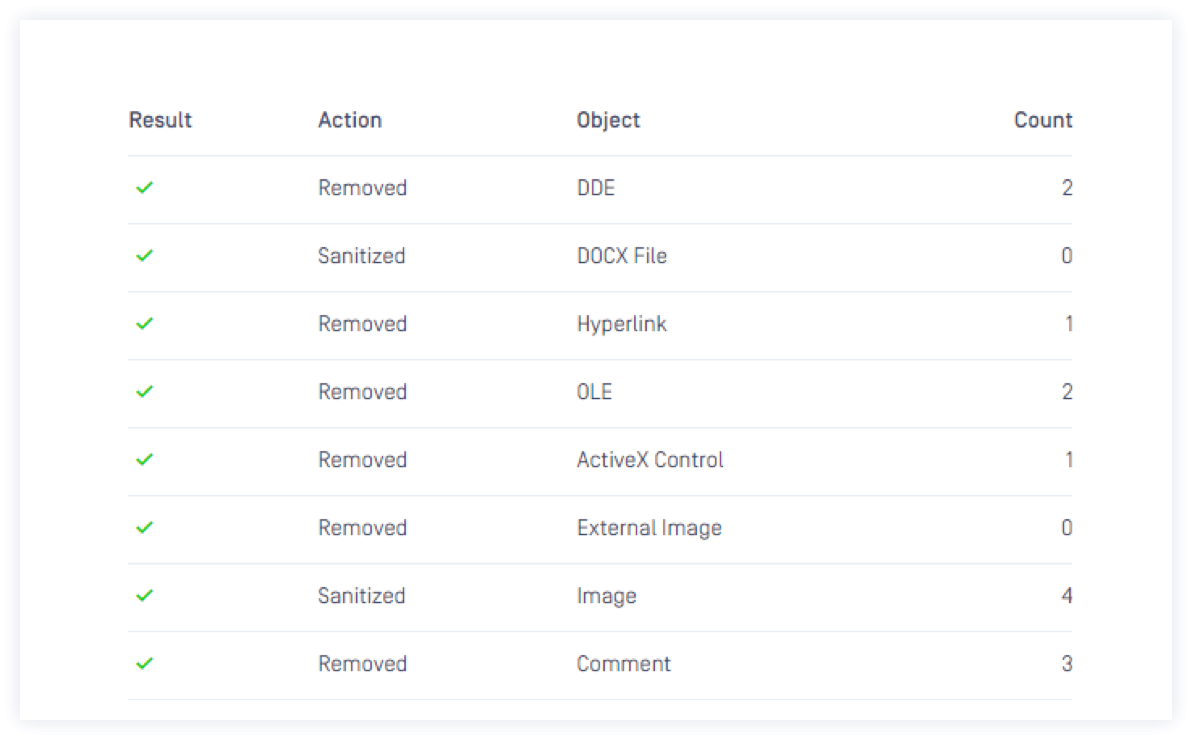
Deep CDR
Prevent zero-day and targeted attacks with OPSWAT’s Deep CDR technology (ranked No. 1 in the industry). We assume that all files are malicious and clean up and rebuild each file, keeping the same visual data with safe content. The technology is highly effective in preventing unknown threats, including targeted zero-day attacks and threats equipped with malware evasion technology.
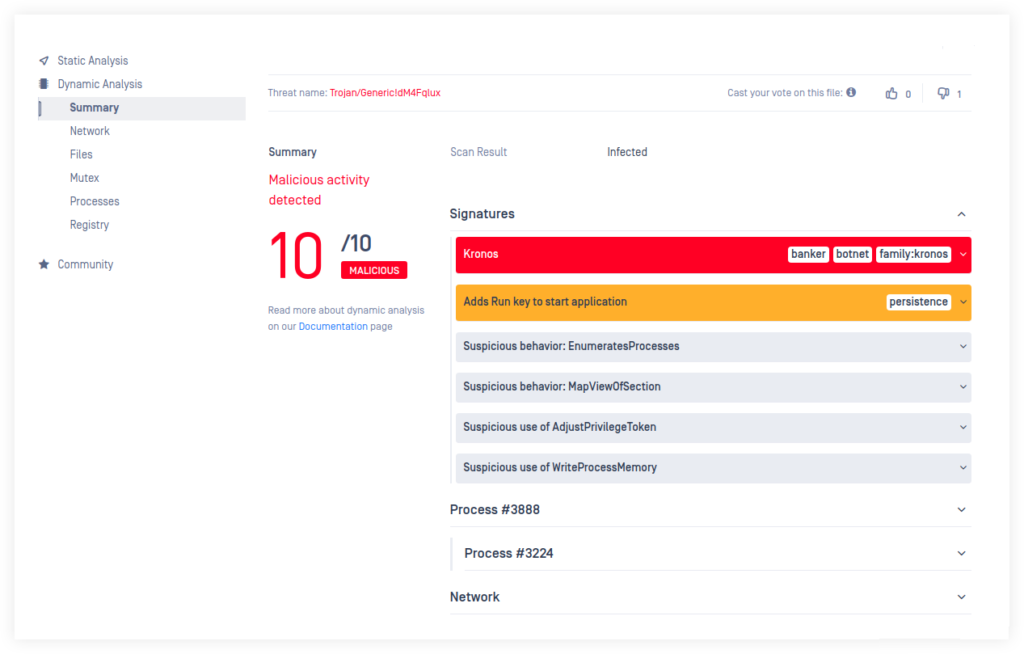
Dynamic analysis in a sandbox
Detonate malware in a controlled environment to expose malicious behavior by recording and classifying file behavior. Not all malware can be detected by static methods such as multiscanning, especially new malware using zero-day attacks. OPSWAT Sandbox extends MetaDefender Cloud’s malware detection capabilities, providing organizations with a complete set of security technology tools.
Rich metadata
MetaDefender Cloud analyzes and extracts rich file metadata, providing file specialists with the The Security Committee accesses information that reveals potential file irregularities or malicious capabilities. This includes Portable Executable information, EXIF data, Android manifest and more.
OPSWAT detects and classifies files based on software vendors and products, and combines the data with a database of security vulnerabilities from NIST and reported data from hundreds of thousands of active endpoints running MetaAccess.

Use Cases
Preventing the transmission of malicious files
Prevent malicious file transfers for web applications that bypass sandboxes and single malware detection solutions.
Deep Content Disarm and Reconstruction (Deep CDR): Disarm more than 90 popular file types and reconstruct each file, providing full usability with secure content.
Scan with more than 20 malware protection engines using signatures, heuristics and machine learning technologies to detect known and unknown threats as early and efficiently as possible.
Quickly and efficiently perform malware analysis
Quickly and efficiently perform malware analysis. Malware analysts can use more than 20 malware protection engines. The MetaDefender Cloud platform is easy to license and provides total data privacy with commercial options that do not store files in the cloud. Your files will be processed privately in a temporary storage location and deleted immediately after the analysis report is completed.

Prevent unknown threats with Deep CDR and Multiscanning
Adding advanced threat detection and prevention features to cyber security products. Reputation functions can also be added to customer solutions. We provide sample code and detailed API documentation to help you get your integration up and running. You can use almost any programming language to leverage MetaDefender’s technology through our APIs, and your developers will prototype with ease.
Complete your threat analysis platform
Threat analysis begins with information gathering. Since 2012, OPSWAT has been collecting malware data from a variety of sources: free users, customers, our OEM community and other cybersecurity vendors. The result is a huge online database of malware shortcuts and malware-related information.
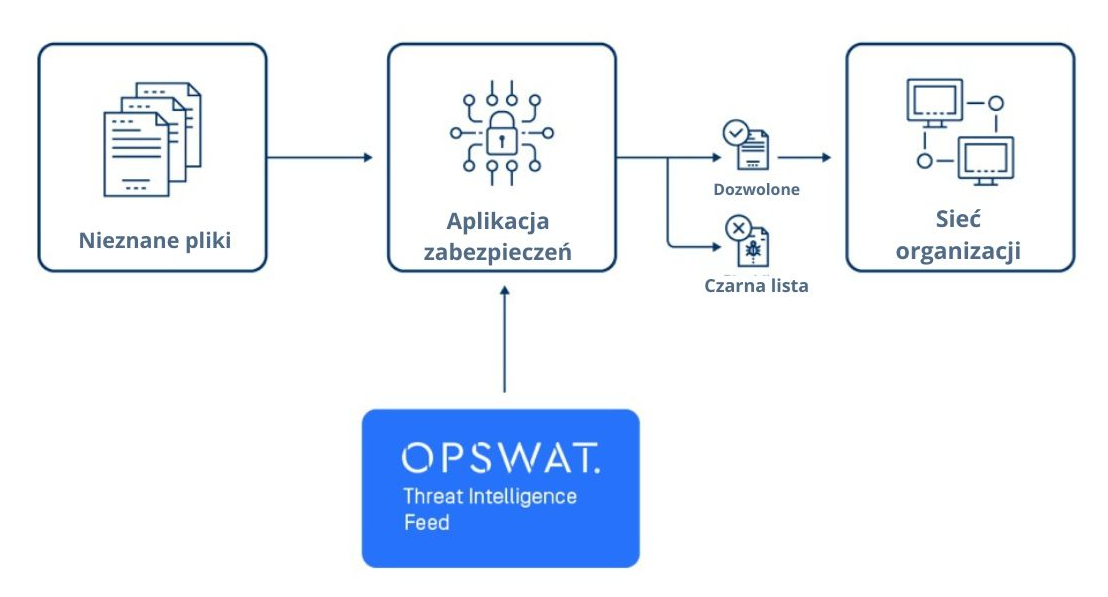
The OPSWAT threat intelligence source enables organizations to leverage real-time malware data collected by the MetaDefender Cloud platform from around the world. Organizations integrate our up-to-date threat intelligence with existing tools or solutions to protect their infrastructure from threats.
THREAT ANALYSIS PLATFORM
Since 2012, we have been collecting file reputation data: multiscanning results and file metadata classified by MD5, SHA1 and SHA256 hashes to create a comprehensive file search service for our users. We offer flexible daily limits, and our REST API is simple and easy to use. We currently have more than 40 billion abbreviations in our database.
We provide live broadcasts for both blacklisted and whitelisted shortcuts, which can also be used in offline environments.
Channels are instantly updated with the latest file shortcuts analyzed by our platform from a variety of sources, including malware programs, client files and more.
Using the same principles of multiscanning, we collect data from multiple online sources in real time specializing in IP addresses, domains and URL reputation to provide a search service that returns aggregated results for our users.
MetaDefender Cloud is also available as a free service for users around the world, including malware analysts and security professionals. Security officials who want to expose hidden malware in files and online locations. We encourage our community to add files and vote for results, and we make this information available to every user.