
Cross-domain solutions
Create a data transfer process that provides
security and trust throughout the structure
How do you secure file transfers across the enterprise, especially for devices you don’t control? Transferring files in and out of secure environments is problematic. Files entering via mobile media and transient devices create opportunities for infection. Stored files may contain zero-day attacks, temporarily unnoticeable and dormant on servers. Allowing files to leave secure environments risks leaking sensitive data.

MetaDefender presentation
BENEFITS
Malware continues to evade existing defenses as cybercriminals create threats of increasing sophistication and businesses implement inadequate protection. Sensitive data can be accidentally stolen or transferred. OPSWAT actively protects sensitive data at every point of transmission.
Many of the specialists in the field. Security allows files to get through to the network after just one virus scan. To detect the latest threats, OPSWAT uses up to 30+ anti-malware engines.
Compliance requirements are designed to minimize breaches and privacy violations. Ensuring compliance is time-consuming and can be costly if requirements are not met.
OPSWAT helps support compliant processes, comprehensive visibility and detailed reporting to help meet the requirements of NERC CIP 003-7, NEI 08-09, NIST 800-53, PCI DSS, RODO, Bulk Power Executive Order 13920 and a wide range of other global regulations.
Borders can be virtual, physical or mobile. OPSWAT securely controls the transfer of files from devices between security levels, systems and physical transfer points.
The global growth of remote workers, BYOD and contractors has resulted in an exponential increase in the number of unmanaged devices. Blindly connecting devices to an internal network or the cloud exposes businesses to serious risks. OPSWAT blocks untrusted devices from accessing physical and virtual environments until they are thoroughly inspected and patched.
Files are vulnerable to infection during transmission. OPSWAT enforces secure file transfer processes, constantly scans for malware and adds digital signatures to ensure file integrity.
The tools work most effectively when combined with conscious decision-making. OPSWAT products introduce simple, efficient processes. Employees will know how to securely enter, store, transmit and extract data across the enterprise while maintaining security compliance. If unsanctioned portable media are intentionally or accidentally introduced into the environment, security processes will block media access to devices and networks.


We offer many products for a wide range of applications – manage security and compliance between domains.
The MetaDefender kiosk acts as a digital gatekeeper - checking all media for malware, security vulnerabilities and sensitive data. The kiosk is designed to be installed at the physical point of entry to secure facilities.
Vault is a secure file storage and retrieval solution that protects critical files. Vault works with the kiosk to provide a secure and effective way to manage threat protection.
MetaDefender Drive is a portable USB-based solution for checking devices for malware, vulnerabilities and sensitive data before they enter or leave an organization. The drive is designed for use where portability is valued and an external network connection is not available.
The OPSWAT client blocks unauthorized use of removable media on all endpoints and scans them for malware before any files are copied to internal systems. The customer can also force the use of any media processed and approved only by MetaDefender Kiosk at the entrance of your organization.
Central management offers a single panel to globally manage multiple OPSWAT deployments, update policies and settings, and monitor the status of all instances in near real-time.

Implementation scenarios
- Standalone MetaDefender Kiosk
- MetaDefender Kiosk for MetaDefender Vault
- MetaDefender Kiosk to OPSWAT Client.
- MetaDefender Vault to MetaDefender Vault
- MetaDefender Drive
- Data diode
STANDALONE METADEFENDER KIOSK
Removable media can be used inside the organization, but must be processed by the MetaDefender kiosk. When the user scans the contents of the media, malicious files will be blocked/deleted, sensitive data may be redacted, and only verified files may remain on the media, which will be moved to safe zones.

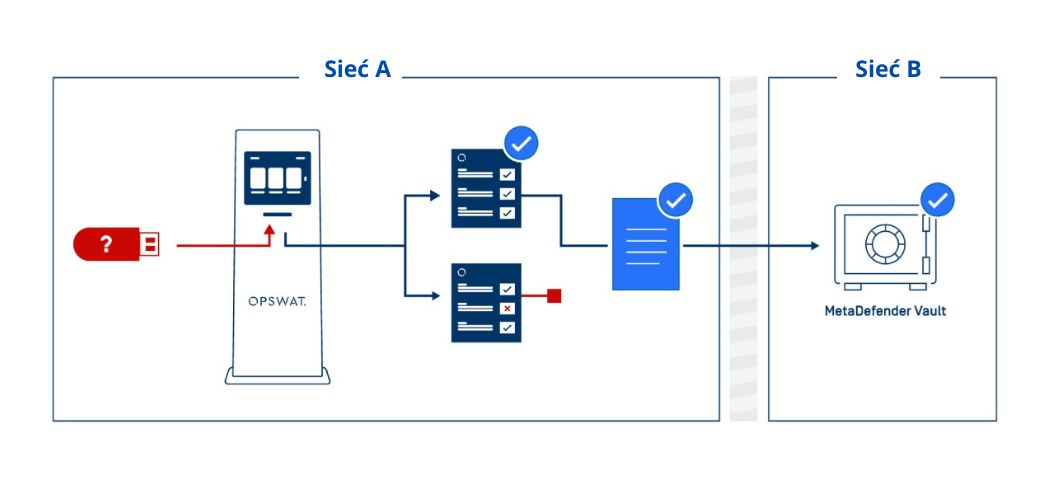
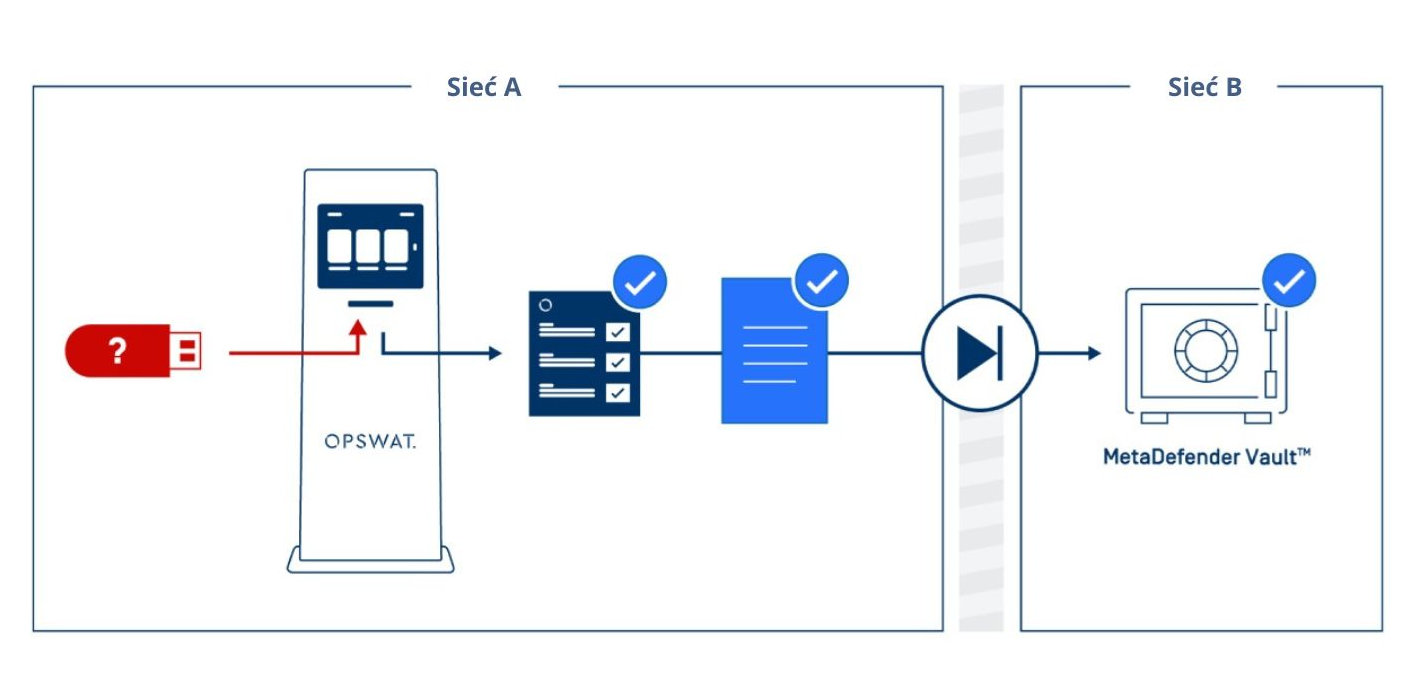
METADEFENDER KIOSK FOR METADEFENDER VAULT
The MetaDefender kiosk is deployed in network segments with low security. Once the user scans the contents of the media, malicious files will be blocked/deleted, sensitive data can be redacted, and only verified files can be transferred to MetaDefender Vault, a secure product for storing and enabling data retrieval from high-security network segments.
Optionally, a data diode can be used to provide one-way data transfer between the Kiosk and Vault. Users can download approved files from MetaDefender Vault to maintain a media-free network environment with a high level of security.
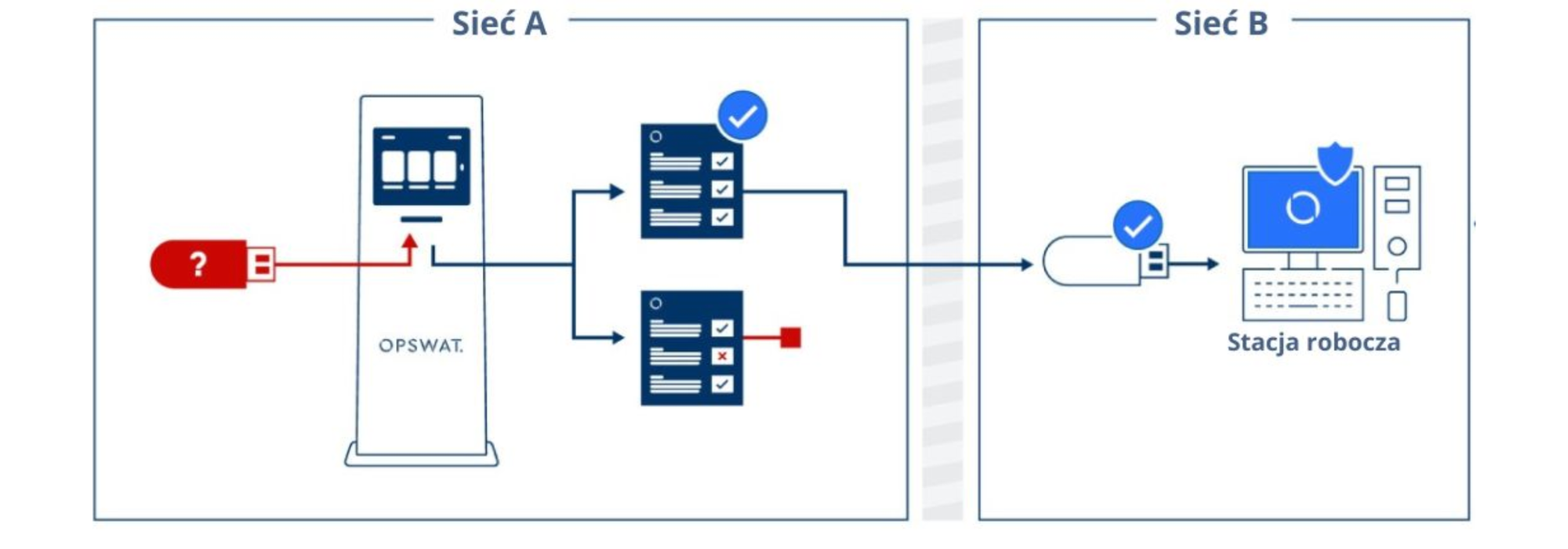
METADEFENDER KIOSK FOR OPSWAT CLIENT
Removable media can be used within an organization, but must be analyzed by MetaDefender Kiosk, and use enforced by the endpoint agent, the OPSWAT client.
When a user scans the contents of the media, malicious files will be blocked/deleted, sensitive data may be redacted, and only verified files may remain on the media, which will be moved to secure areas. If an unauthorized removable media is brought into the organization and placed on the OPSWAT customer’s protected devices, the unverified media will be completely blocked.
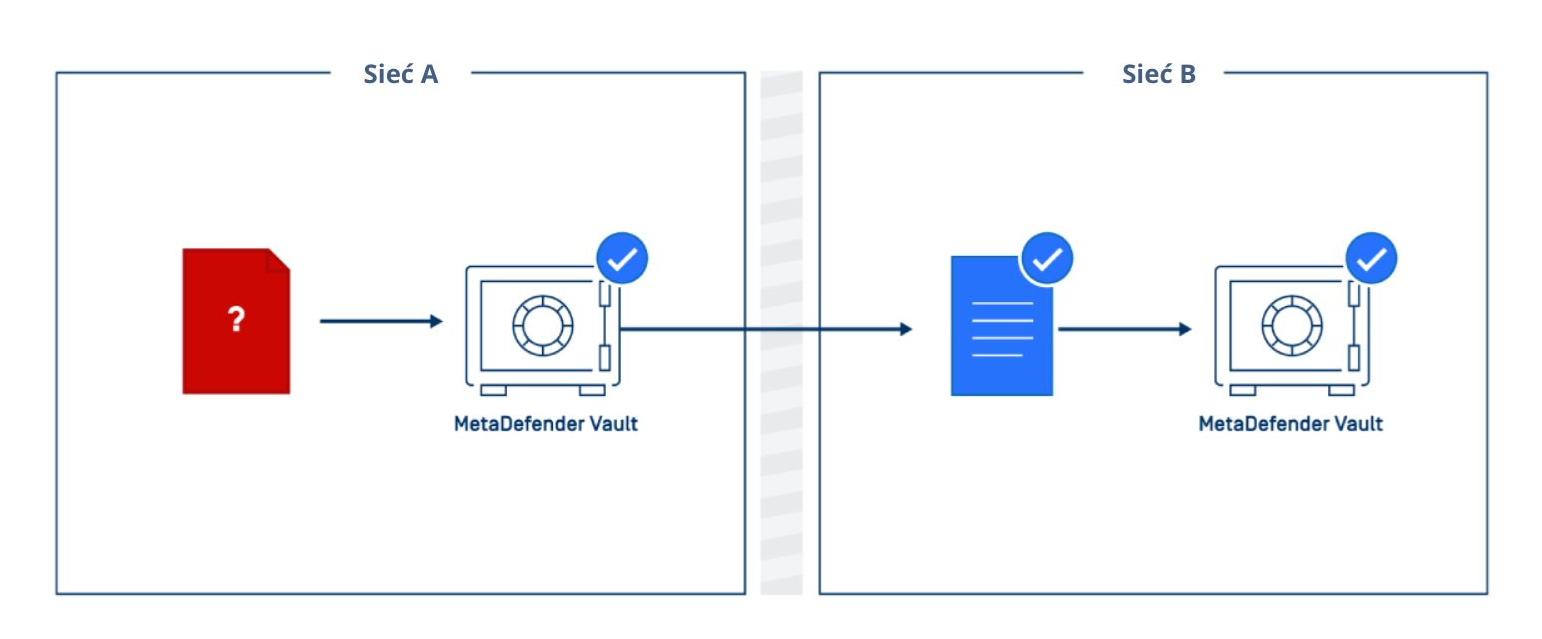
METADEFENDER VAULT TO METADEFENDER VAULT
MetaDefender Vault (forwarding side) is deployed in network segments with low security. All users can use web browsers to visit the Vault landing page and log in with credentials or guest ID to upload files via
All content will then be scanned by MetaDefender Vault (the transferring side): malicious files will be blocked/deleted, sensitive data can be redacted, and only verified files can be transferred to a second MetaDefender Vault (the receiving side), usually high-security network segments. Once uploaded, files can be continuously scanned for outbreaks before being made available for download unless approved by supervisory controls.
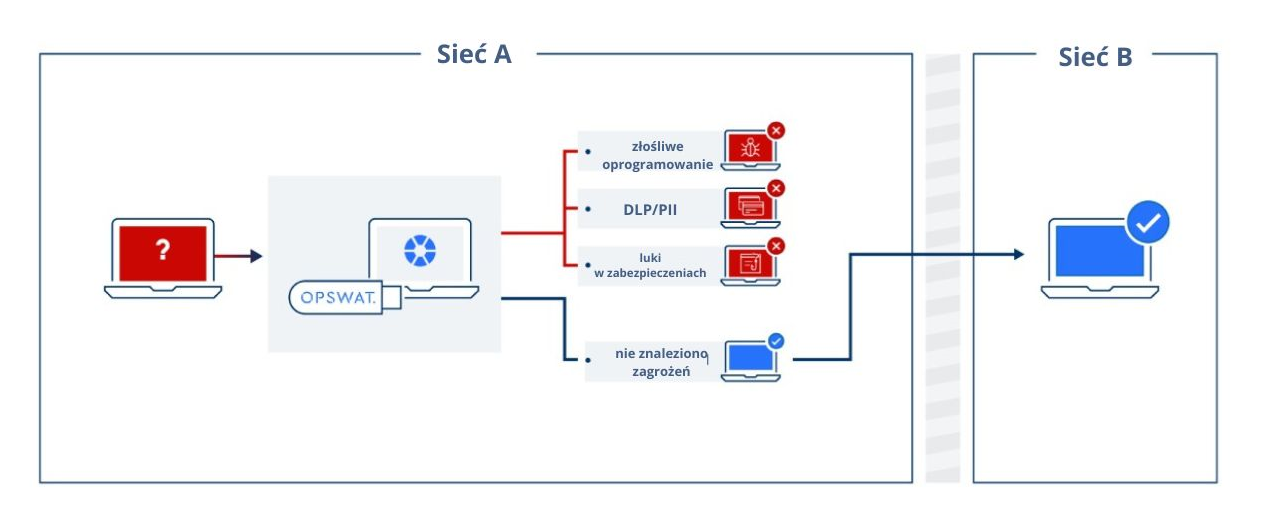
METADEFENDER DRIVE
When any transient devices, such as borrowed laptops, resources returned by current employees, subcontractor machines, etc., Return to a high-security network, MetaDefender Drive can be used to scan assets for the risk of malware, loss of sensitive data, vulnerable binaries and installers, and applications created by foreign adversaries.
After a thorough inspection of the device, a detailed approval report will summarize which assets can be let in.
DATA DIODE GUIDE
A data diode is a hardware-based cybersecurity solution that provides one-way information transfer between two networks. Data diodes have been common for decades in high-security environments such as defense facilities and intelligence agencies. With the growth of the industrial Internet of Things and digitization, data diodes are increasingly being deployed by private enterprises to securely transmit data generated by the industrial control and safety systems of nuclear and other power generation plants, manufacturing facilities and transportation systems to other networks ( including the public Internet), while protecting the networks containing these systems from attack.
Unidirectional means that data can only travel in one direction. A sensible way to think about data diodes is “one-way data valves,” allowing data to flow without return. A typical scenario is when a data diode provides a one-way transfer from a high-security network to a lower-security network. Data can be transmitted while the high-security network remains protected from attack using this connection. In this scenario, the diode protects systems on a high-security network that produce transmitted data.
Trust no file. Trust no device.



